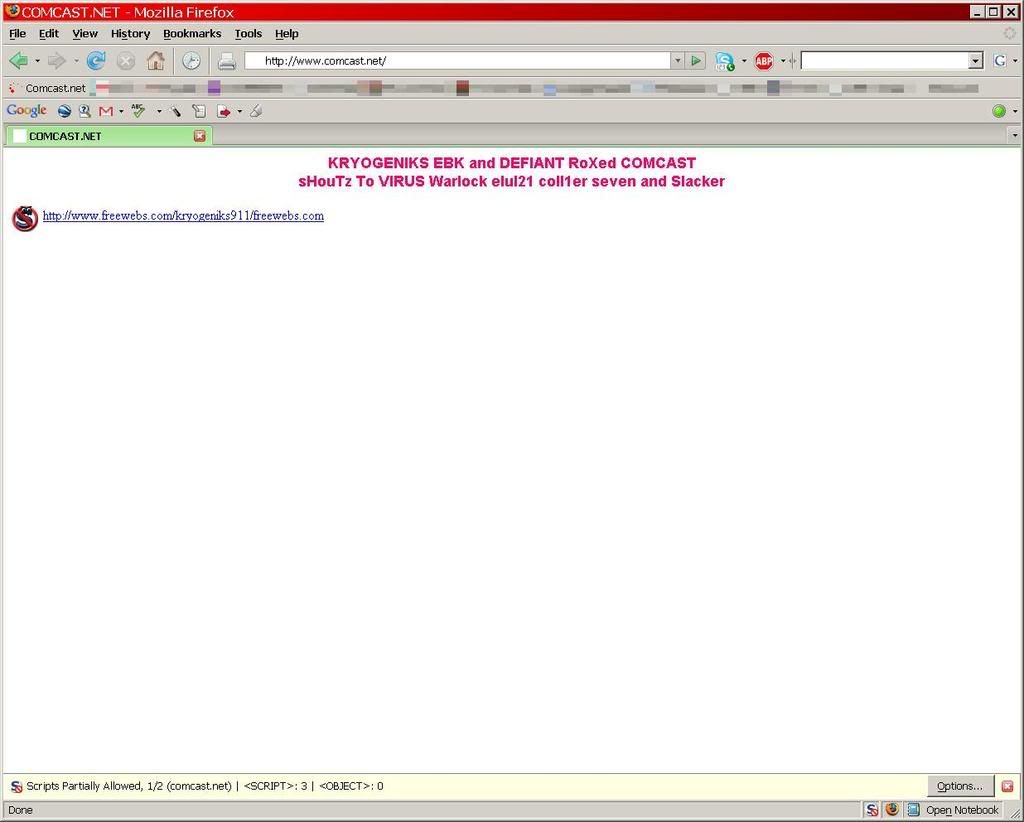
I just tried to log into my Comcast webmail and was greeted by the following at the Comcast.net main URL:
It looks like KRYOGENIKS EBK and DEFIANT are looking for credit on this hack.
Thankfully I have ‘NoScript‘ installed as a plugin for my Firefox browser to minimize the exposure I would get when something like this happens. I don’t know if a malware script was really trying to run or the URL would be malicious to my windows box if I followed it, but why tempt fate?
Too bad for Comcast…
[Update] – Apparently this is not seen by those Comcast customers using Comcast DNS servers. I use OpenDNS servers, so this may not be a complete breach of Comcast.net servers in as much as some name servers. I found a thread on DSLReports regarding the issue and a Comcast employee and forum member (Michael2) has been feeding information about the issue as it develops to forum members there. I’ll be checking it again at irregular intervals as the drama unfolds.
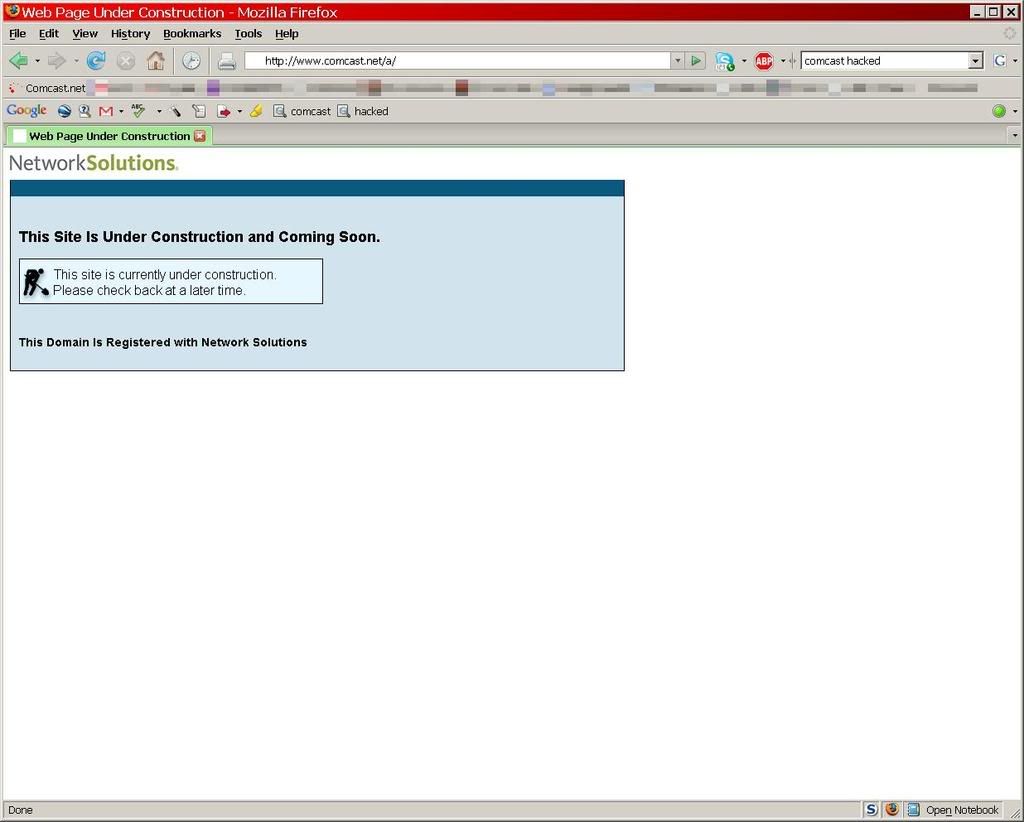
[Update 2] – I checked again (now) at 10:15pm PT and noticed what a commenter on Digg.com is seeing. Comcast apparently regained a bit of control and is redirecting to a subdirectory with an “Under Construction” page:
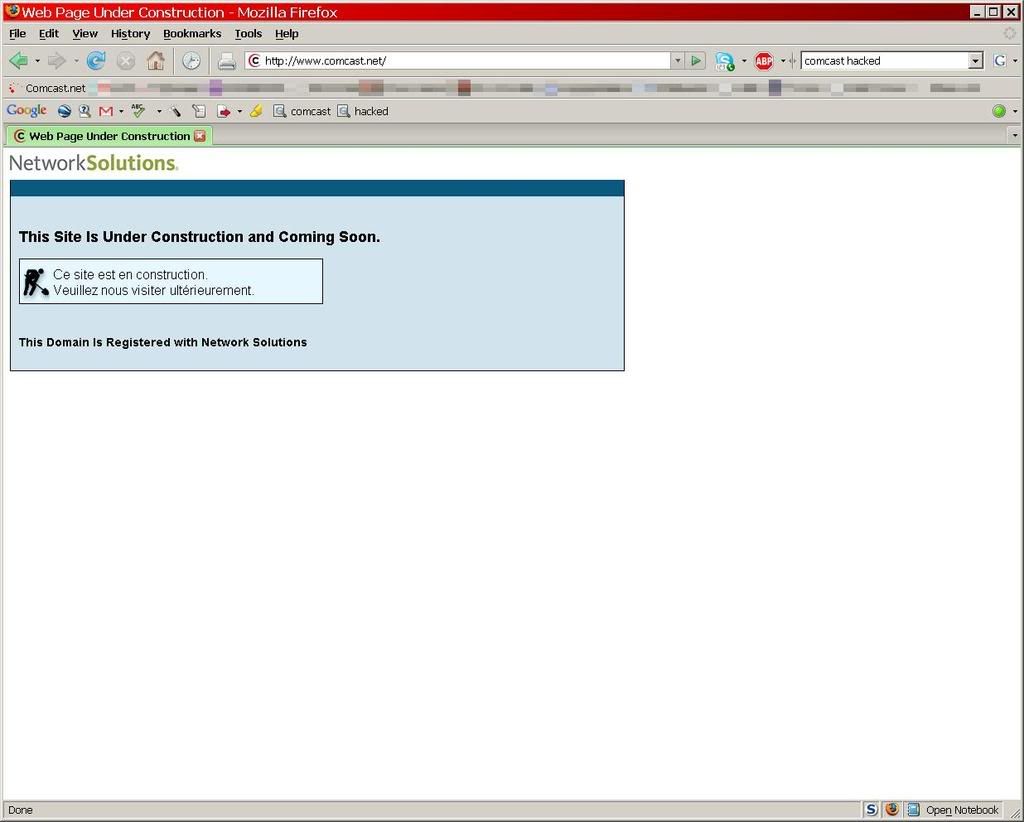
[Update 3] – As of 11:20pm PT Comcast seems to be making progress. Now the primary URL has the “Under Construction” page:
[Final Update] – As of this morning (Thursday) it appears that Comcast has regained control of their domain and it’s back to business as usual. Time to change passwords, just in case.
[Post Final Update] – Wired was able to manage an interview and post it late Thursday night of the two kids that perpetrated the pointless hack. If you’re interested in reading what a couple talented, but ultimately aimless kids were thinking not thinking, then here you go…
/drama